Authenticity II: Digital Methods
Two Pillars of Digital Authentication
- ENF Analysis = physical truth anchor
- Links the recording to real-world time, place, and grid conditions
- Metadata Consistency = digital integrity check
- Verifies the file’s lifecycle from creation to present
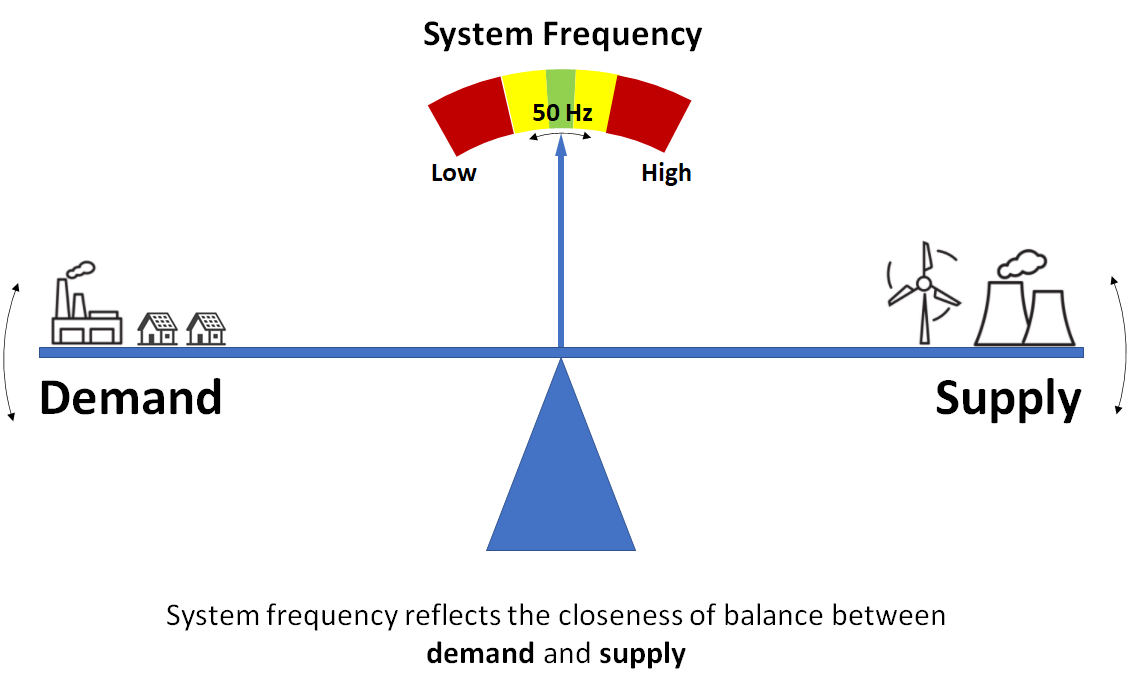
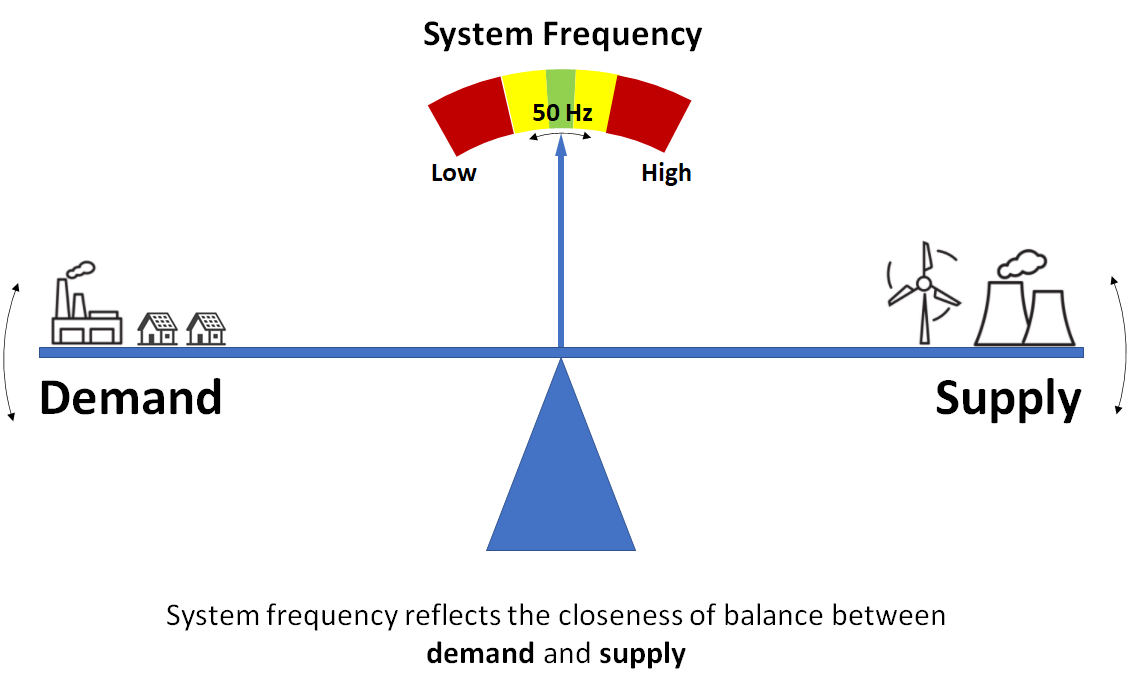
What is ENF?
- Electric Network Frequency: the supply frequency of the power grid
- Nominally 50 Hz (Europe, Asia, Australia) or 60 Hz (North America)
- Fluctuates randomly as operators balance supply and demand
- Fluctuations are unique to a specific time and consistent across an entire grid
Why Does ENF Fluctuate?
How ENF Enters Audio Recordings
| Pathway | How it works |
|---|
| Electromagnetic induction | Mains hum induced into audio circuitry or cables |
| Acoustic coupling | Microphone picks up hum from transformers/motors |
| Direct connection | ENF enters through wall outlet power supply |
The ENF Extraction Pipeline

Step 1: Decimation
- Audio recorded at high rates (e.g., 44.1 kHz) but ENF is low-frequency
- Downsample to ~300–400 Hz to focus on the band of interest
- Apply anti-aliasing FIR low-pass filter before decimation
- Reduces computational load dramatically
Step 2: Bandpass Filter
- Isolate the nominal frequency range (e.g., 49.5–50.5 Hz for a 50 Hz grid)
- Sharp FIR bandpass filter removes everything outside this narrow band
- What remains: the ENF signal plus any noise in that frequency range
Step 3: STFT Analysis
- Divide signal into overlapping frames (typically 8–16 seconds)
- Apply a window function (Hann or Blackman-Tukey) to each frame
- Compute FFT for each frame to find the dominant frequency
- Zero-padding (often 4×) improves frequency resolution
Resolution vs. Frame Length Tradeoff
- Longer frames (16–32 sec): better frequency resolution, poor time resolution
- Shorter frames (1–2 sec): capture sudden changes, but frequency “blurring”
- This is the Heisenberg uncertainty principle applied to signal processing
- Typical forensic choice: 8–16 second frames as a compromise
Step 4: Peak Detection and Interpolation
- Find the highest-magnitude FFT bin in each frame — this is the ENF estimate
- True frequency usually falls between bins
- Quadratic interpolation (QIFFT) refines the peak to sub-bin precision
- Concatenate all frame estimates → the ENF trace
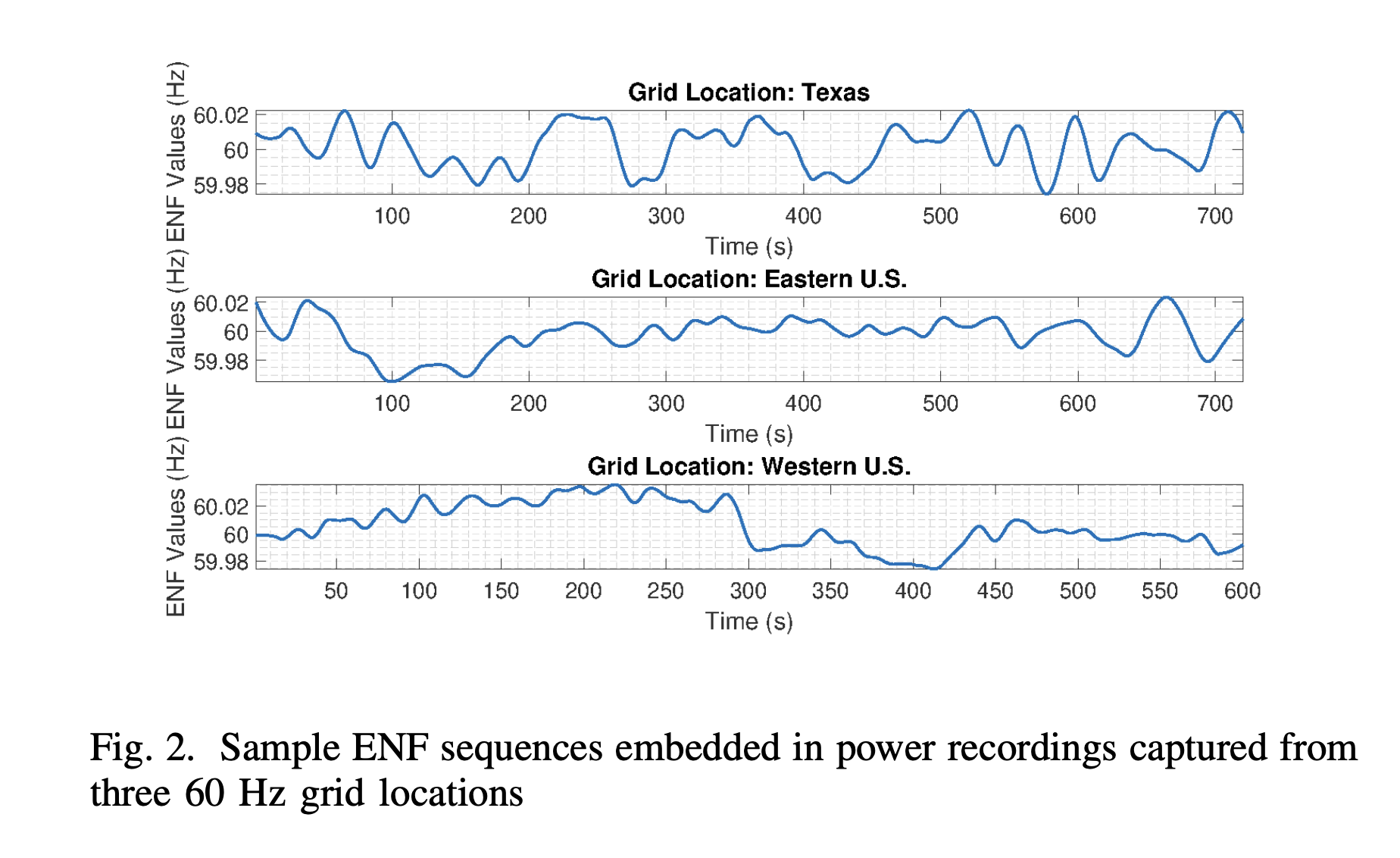
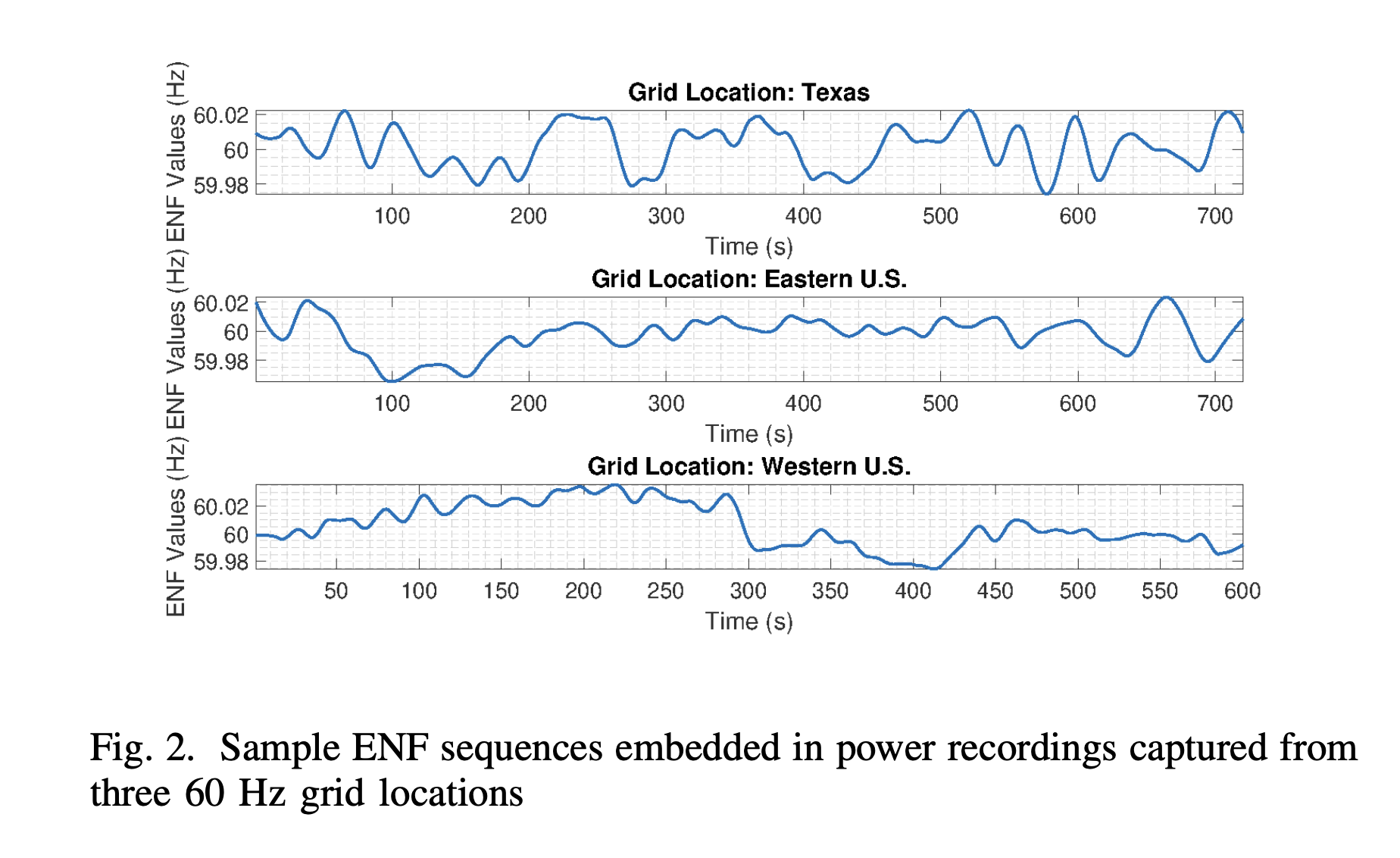
ENF Trace Example
Beyond STFT: Parametric Methods
- MUSIC: eigendecomposition of autocorrelation matrix; exhaustive spectral search
- ESPRIT: uses rotational invariance; faster and more robust than MUSIC
- Both offer higher resolution than STFT but assume a signal model
- STFT remains the standard for most forensic work
ENF Harmonics
- The fundamental (50/60 Hz) may be filtered out by communication systems (>300 Hz cutoff)
- Harmonics at 100, 150, 200 Hz etc. can survive
- Multi-Harmonic Combining (MHC): analyze multiple harmonics for better robustness
- Some systems examine up to the 116th harmonic
ENF Reference Databases
Authentication: Matching Against the Database
- Extract ENF trace from the recording
- Normalize both trace and reference to zero mean, unit variance
- Slide the trace across the reference database sample by sample
- Measure similarity with correlation coefficient or MMSE
When is a Match Statistically Significant?
- Grids have daily cycles (morning surges repeat) creating self-similarity
- A Monday morning pattern may randomly resemble another Monday
- Recordings <10 minutes are highly susceptible to false positives
- SNR is critical: low SNR causes rapid increase in matching errors
Timestamping: The Cracow Case
- 2003 Poland: disputed recording of two businessmen
- Device clock was off by nearly 200 days vs. witness testimony
- ENF trace matched the time claimed by witnesses, not the device clock
- ENF provided the objective physical evidence to resolve the dispute
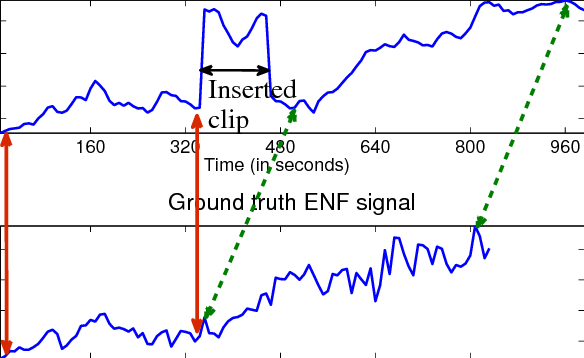
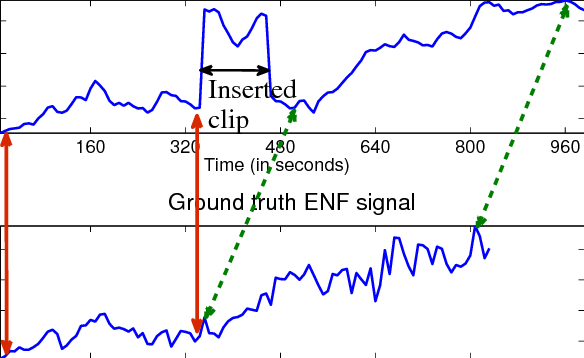
Tampering Detection via ENF
- Splicing creates discontinuities in the ENF trace
- Phase jumps: sudden shifts in wave position (detectable at millisecond level)
- Frequency jumps: sudden changes in the ENF value between frames
- Natural grid fluctuations are slow and continuous; edits create abrupt breaks
Inserted Clip Example
ENF in Video
- Artificial lights flicker in sync with the power grid
- Flicker occurs at 2× grid frequency (100 Hz or 120 Hz) — both AC half-cycles produce light
- Invisible to humans, but captured by camera sensors
ENF for Geolocation
- Inter-grid: Which power grid was the recording made on?
- US Eastern, US Western, European grids have independent frequency patterns
- Intra-grid: Where within a specific grid?
- Frequency varies slightly by location due to local load conditions
Localization Within a Power Grid

Limitations of ENF Analysis
- Weak signal: ENF is often 40–60 dB below primary audio content
- Short recordings (<10 min): self-similarity creates false positive risk
- In-band interference: voices and music in the 50/60 Hz range corrupt the trace
- Clock skew: device clocks drift, complicating alignment
ENF Anti-Forensics: The Threat
- Attackers can use a notch filter to erase the original ENF signal
- Then re-embed a forged donor signal from a different time/location
- Forged signals can achieve correlation scores up to 0.96 — visually convincing
Detecting ENF Forgery
- Forged signals leave traces in high-frequency spectral content
- Subtle phase inconsistencies where the synthetic tone blends with the audio
- Recapturing (playing and re-recording) embeds two overlapping ENF signals
- Examiners use decorrelation algorithms and deep learning CNNs to detect these
- Internal metadata: embedded in the file container (headers, encoding info, device tags)
- External metadata: maintained by the OS (file system timestamps)
- Together they form a digital audit trail of the file’s lifecycle
- Acquire and hash: secure the original, create a bit-stream copy, generate MD5/SHA256
- Technical assessment: document format, codec, sample rate, bit depth, duration
- Global audit: use multiple tools to extract all metadata fields
- Exemplar creation: record test files on the same device model for comparison
- Local discontinuity check: examine waveform and spectrogram for anomalies
Hash Verification
- MD5 or SHA256 hash computed immediately upon acquisition
- Creates a unique digital fingerprint of the file’s exact contents
- Any change — even a single bit — produces a completely different hash
- Piecewise hashing: verify integrity of specific file segments independently
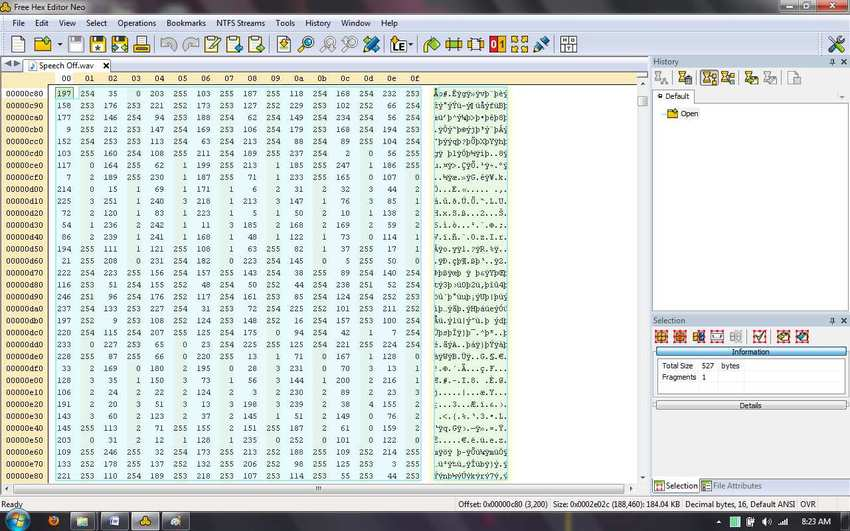
Hex Editor Analysis
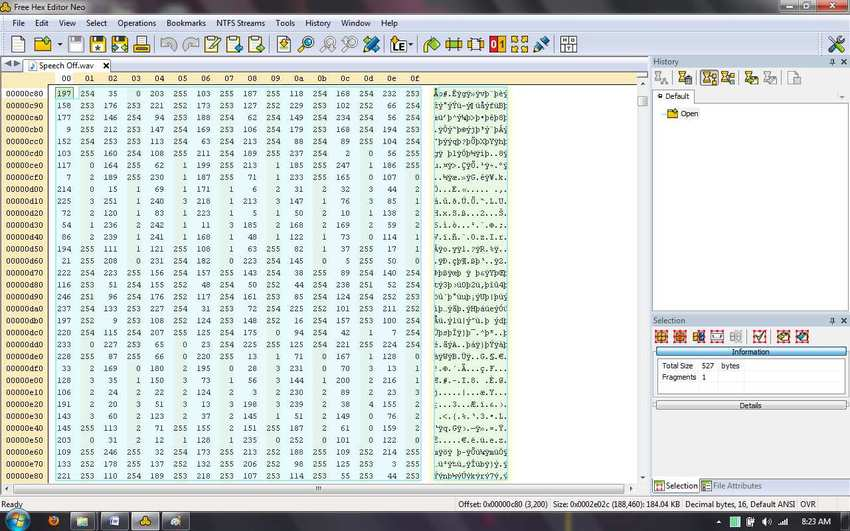
- WAV: RIFF chunk structure; uncompressed PCM; manufacturer data in custom chunks
- MP3: ID3 tags (v1 at end, v2 at beginning); frame-based structure
- AAC: Common on smartphones (iPhone default); M4A container
- WMA: Microsoft proprietary; ASF container with device-specific metadata
Manufacturer Signatures
- Recording devices embed proprietary hex strings in file headers
- Olympus: “OLY”, “mp3”, “702” (model number) at specific offsets
- These signatures are like a device fingerprint
- Editing software overwrites these signatures with its own tags
The Olympus Example

Encoding Parameters as Evidence
- Sampling rate (44.1 kHz, 48 kHz, 8 kHz)
- Bit depth (16-bit, 24-bit)
- Codec (PCM, AAC, MP3, DSS)
- Channels (mono, stereo)
- Mismatches between claimed origin and encoding = evidence of re-encoding
Device Fingerprints: Smartphones vs. Recorders
- Smartphones: GPS coordinates, AAC codec, mobile-specific metadata fields
- Dedicated recorders: proprietary codecs (DSS), manufacturer hex strings, serial numbers
- Computer recordings: lack physical environment markers, show desktop software signatures
- Double compression artifacts appear when re-encoding a lossy format
- Standard tool for extracting metadata from audio/video files
- Key fields: Create Date, Modify Date, Make, GPS, Compressor Name
- Can extract EXIF, IPTC, XMP, and format-specific metadata
- Also used to test vulnerabilities — can metadata be injected or modified?
Timestamps and MACB
- Modification: last time file content changed
- Access: last time file was opened
- Creation: when the file was first created on this volume
- Entry modification (B): when the MFT record was updated
- Stored in the NTFS Master File Table ($MFT)
Detecting Timestomping
- Timestomping: manually changing a file’s creation or modification date
- Attackers alter $MFT timestamps to match a false narrative
- System journals ($LogFile, $UsnJrnl) record file operations independently
- Comparing MFT timestamps against journal entries reveals the forgery
Software Fingerprints
- Editing software overwrites manufacturer metadata with its own tags
- Adobe Audition inserts XMP metadata identifying the software version
- Audacity, Pro Tools, and other DAWs leave similar traces
- The absence of expected manufacturer metadata is itself a red flag
- Metadata documents the file’s complete lifecycle
- Hash at acquisition → hash at every handoff → hash at analysis
- Any break in the chain or hash mismatch = compromised evidence
- Embedded checksums in proprietary formats provide additional verification
Part 3: Putting It Together
- ENF: links the file to the physical world (time, place, grid)
- Metadata: verifies the digital lifecycle (device, software, timestamps)
- When they agree → strong evidence of authenticity
- When they disagree → strong evidence of tampering
Resolving Ambiguity
- Short recordings: ENF alone may have multiple matches → metadata narrows the timeframe
- Forged metadata: timestamps easily changed → ENF provides independent physical check
- Clock skew: device clock drifted → use ENF as a time anchor to calculate the offset
- Missing ENF: outdoor/battery recording → metadata may be the only evidence available
The DEMA System
- Decentralized ENF-based Media Authentication for social media
- Aggregates ENF data from edge nodes and cloud servers
- Uses blockchain (Proof-of-ENF consensus) to prevent database poisoning
- Cross-references EXIF GPS/timestamps against ENF databases
Case Integration Example
- Recording claims to be from March 5, 2:15 PM, New York office
- Metadata check: iPhone AAC, creation date March 5, GPS coordinates match office
- ENF check: trace matches US Eastern grid reference at March 5, 2:12 PM
- Clock skew: 3-minute offset consistent with typical iPhone clock drift
- Conclusion: evidence supports authenticity
Summary
- ENF analysis extracts power grid frequency to verify time, location, and integrity
- Metadata consistency audits file headers, encoding, and timestamps for modification
- Neither method is sufficient alone — use both as complementary pillars
- The field faces an arms race between forensic tools and anti-forensic techniques